Publicly disclosed code for a critical Linux vulnerability known as CopyFail, tracked under CVE-2026-31431, has raised alarm bells within the cybersecurity community. This exploit allows attackers to gain root access to numerous Linux distributions, including data center servers and personal computers. While patches for the vulnerability were made available for certain Linux kernel versions, many distributions had not integrated these fixes at the time of the exploit’s release.
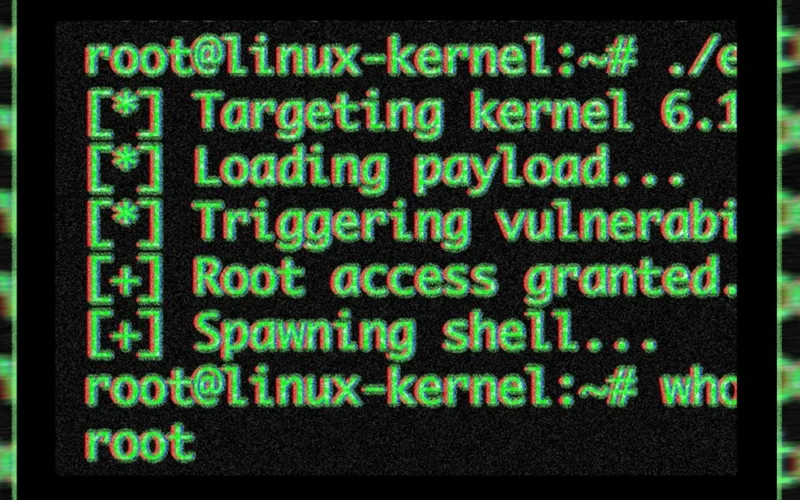
The vulnerability stems from a local privilege escalation flaw, enabling unprivileged users the ability to elevate their status to administrators. The exploit relies on a single piece of code that works across multiple Linux distributions without any modifications. Thus, an attacker who can execute unprivileged code on a machine can easily promote themselves to root, gaining the ability to read sensitive files, install backdoors, monitor processes, and potentially access other systems.
Researcher Jorijn Schrijvershof stressed the significance of this vulnerability in shared infrastructure scenarios. Because it allows elevation of privileges across various systems sharing the same Linux kernel, the consequences can be devastating, especially for multi-tenant environments like cloud services and containerized applications. For instance, if an attacker gains access through a known vulnerability in a web application, they can then leverage CopyFail to achieve root access, compromising every other tenant on the same host.
The flaw arises from a logic issue in the Linux kernel’s crypto API, making it particularly dangerous. Unlike many vulnerabilities that rely on memory corruption or race conditions—often less reliable and inconsistent across kernel versions—CopyFail’s exploit works consistently across all affected distributions without any special timing requirements. This reliability poses a realistic threat, leading experts to classify it as one of the most severe vulnerabilities in recent years.
The revelation about CopyFail drew comparisons to other notorious Linux vulnerabilities such as Dirty Pipe from 2022 and Dirty Cow from 2016, both of which were actively exploited. Compounding this issue is the fact that many Linux distributions tend to use older kernel versions, applying patches retroactively. Although some distributions, such as Arch Linux and RedHat Fedora, have released patches, the majority have not yet addressed the vulnerability.
The exploit was uncovered by Taeyang Lee at Theori, who noted that the vulnerability could be identified through their AI-powered security tool within just an hour. In addition to being a local privilege escalation flaw, CopyFail can also potentially breach Kubernetes containers.
Given the high severity of CopyFail and its potential for active exploitation, all Linux users are urged to check their systems immediately and apply vendor patches as they become available. For further information, affected users should consult their respective Linux distribution vendors and follow their mitigation guidance.